In my previous blog post Upgrade from VMware Horizon 7.13.1 to 8.6 (2206) fails with VMware Horizon View Blast Secure Gateway (VMBlastSG) could not be installed. In this post, I will go into the details on the manual uninstall process and installation of the latest version of the VMware Horizon.

Why inplace upgrade fails?
The core reason for the in-place upgrade failing was that the VMware Service around Horizon was not getting deleted during the uninstall performed by the setup, which was rolling back the change.

What is the solution?
The quick solution is to uninstall the VMware Horizon 7 HTML Access, followed by VMware Horizon 7 Connection Server. Perform a reboot on the broker virtual machine, and this step will delete the services from about that were not getting deleted automatically. Install the VMware Horizon 8.x setup, and the installation will go smoothly.

What is the alternate method detailed steps?
The in-place upgrade method described here – Upgrade Connection Servers in a Replicated Group works 99.99% of the time in corner cases like mine. You will have to perform this method. Ensure you follow the basics of a full backup of the brokers, ADAM database, SQL database, backup of the locked.properties file and Disable vCenter provisioning.
Don’t perform this method without seeking proper VMware Support guidance. If you run into issues, you will be in unsupported territory and might ask yourself how you ended up here.
Uninstall existing VMware Horizon
- Login to the broker you are going to perform the upgrade and open the Programs and Features
- First, uninstall the VMware Horizon 7 HTML Access
- Second, uninstall the VMware Horizon 7 Connection Server
- You will be left with the AD LDS Instances (Local and CloudPod partitions). Make sure you leave them as-is.

Reboot
To get rid of the ghosted services perform an reboot of the broker VM.
Install the latest release 8.x
- Login to the broker you are going to perform the upgrade
- Validate whether the above services are deleted
- Right click and run as administrators on the Connection server.exe of the 8.x setup
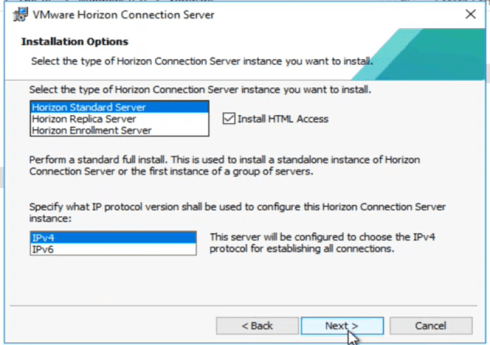
- Make sure you select – Standard Server and click on HTML access and IPv4
- It will detect the instance of the Horizon and you need to click on OK

- Select Configure the Firewall within Windows
- The Horizon 8.x will be installed successfully on the virtual machine
- Repeat this steps on the other brokers within your POD
Validations
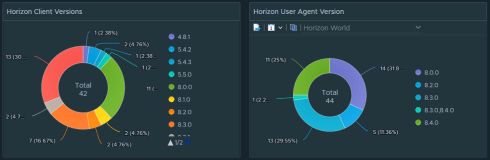
You must wait approximately 5-7 mins for the Horizon Administrator console to come online. Validate the Health dashboard for any errors and check the desired 8.x version is present.
I hope you will find this information useful if you encounter the issue and it should help you save time. If you manage to tweak or improvise further on this solution, please don’t forget to keep me posted.
Thanks,
Aresh Sarkari


























Recent Comments